Core Responsibilities
-
CSOs or CISOs need to stay ahead of all types of attacks or vulnerabilities that could be harmful in terms of a breach or areas that weaken security. Once identified, they also have the core responsbility of finding ways to eliminate these threats.
CSOs also need to direct their team to monitor the flow of data information and spot when anamolous amounts of data are leaving the company.
In addition to guiding their team in terms of a response to an incident, more importantly is the implementation of proactive methods to avoid its occurence in the future and inclusion within the corporate security policy. SecOps teams typically get overwhelmed with security related alert storms and spend more of their day finding that "needle in the haystack", which basically means the security threat that impacts Revenue, Productivity or Reputation. This makes it very critical for security teams to quickly identify threats that are impacting the business-critical applications in a timely manner.
Eliminate Pain Points for your Team
-
As the primary leader for the security teams, it is very important for CSOs to
eliminate the critical pain points for the team. Leading pain points include:
- Alert Fatigue
- Bogged down by day to day management tasks
- Too many resources spent in documentation and reporting, instead of focusing on solving the problem
- Working late hours, as current monitoring techniques and tools are not efficient
- Co-ordinating (Finger-pointing actually!) with IT Operations teams due to inconsistent visibility
- Focus on alerts that are impacting the business-critical application
- Reduce the Mean Time to Identification of the threats
- Provide a correlated view for all teams within the IT organization (NetOps, SecOps, ITOps, DevOps) to figure out the root cause behind the application outage or slowdown and eliminate expensive and stressful war room conversations.
These pain-points can be eliminated by practices and tools that help the team:
The Changing Threat Landscape
-
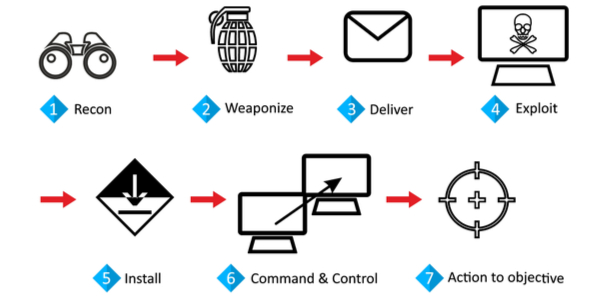
Most enterprise organizations rely on legacy security monitoring practices, that include perimeter security and endpoint protection. But threats these days bypass traditional monitoring solutions and sneak inside the Data Center or the Cloud deployment.
The Threat Landscape in this day and age has also evolved dramatically from the
traditional "grab and dash" as well as mass "spray and pray" exploitation
practices to more sophisticated and patient attacks that impact business
operations for any enterprise organization like never before.
The attacker after breaching the north-south traffic perimeter, conducts internal reconnaissance, gains access to the outside world using Command and Control and then executes its objective which could include stealing of valuable data or bringing down a mission critical service in a stealth manner by moving laterally within the Data Center. This makes lateral or east-west traffic monitoring for any Hybrid Enterprise, the most critical area that needs to be monitored.
Also security teams have limited resources and may not own the right tools that give them the visibility, thus limiting their contribution. This challenges the heavy investement the organization may have already made in the IT infrastructure and security.
According to the 2019 Verizon Data Breach Report, even though external sources account for most of the threats launched against the organization, Internal threats contribute to the most compromised data. This makes the identification of Malicious Insider Threats more critical for SecOps teams.
Proactively Detect Advanced Malicious Threats in Real-Time for Data Center and Cloud Workloads
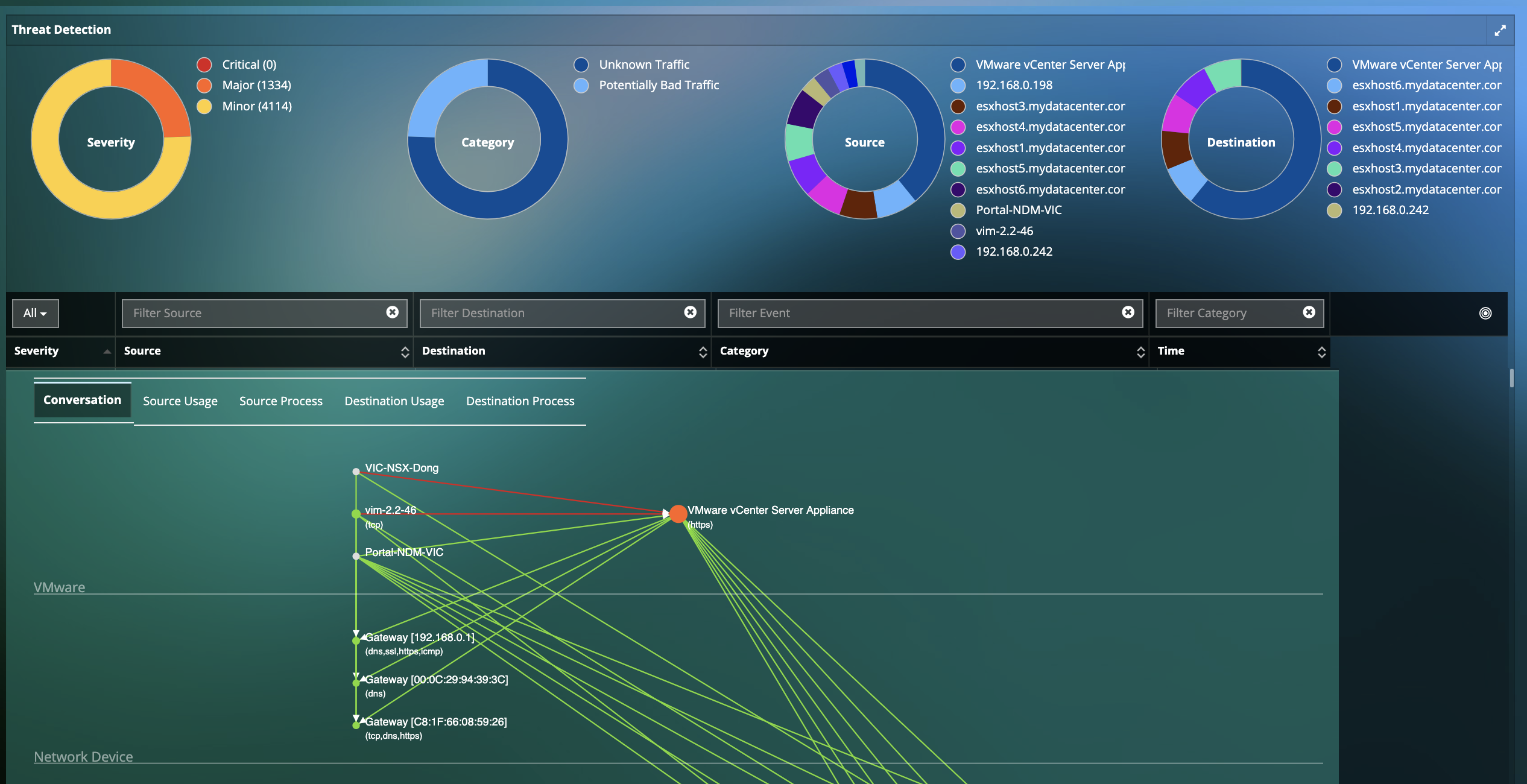
- Real-time Detection for thousands of Advanced and Persistent threats including Malware, Exploit Kits, Webshells, Port Scans, SMB Probes, Information Leakages, Obfuscation, OS fingerprinting, and many more. :
- Latest threat rules support and updates from the largest group dedicated to advances in the network security industry.
- Insights into historical context of the origins of threats, even across cloud boundaries.
- Unique insights into Dependencies and Infrastructure associated with threat.
- Rich Threat Intelligence with detailed Information on impact, systems affected, CVE information, corrective actions, etc.
- Prioritize your team's efforts with visibility into the Top Exploited Hosts.
Manage Unauthorized Data Exfiltration
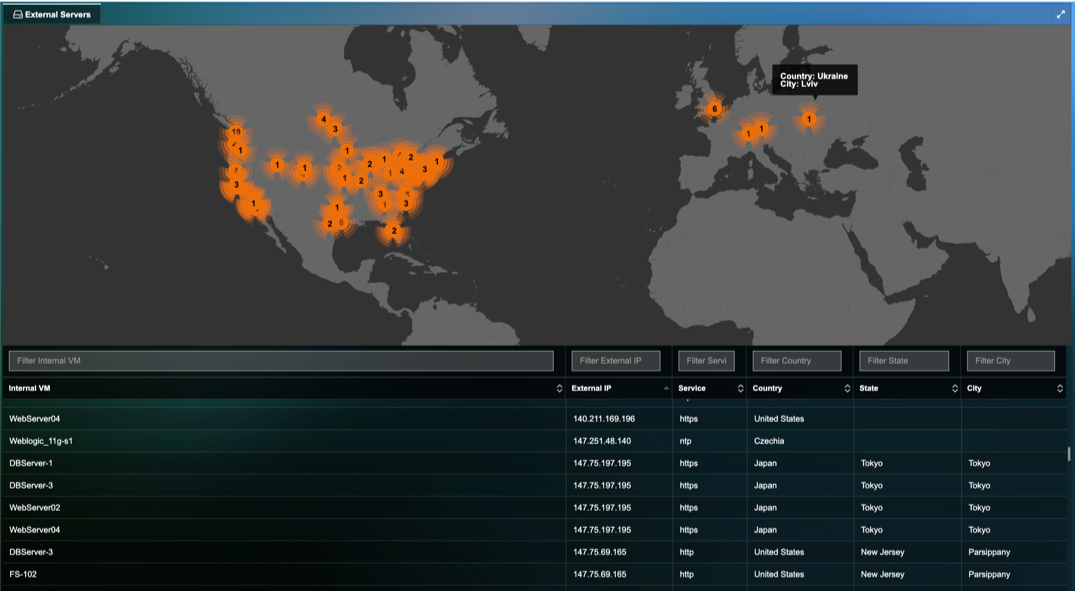
- Reduce Risk associated with outbound connections with immediate visibility into Traffic Exfiltration from your deployment to unauthorized or malicious locations.
- Visualize Outbound traffic details on a world map including Internal VM details, Destination IP, Destination Server location, Application/Service for the outbound traffic, etc.
- Conclusive chain of evidence with Application Transaction information.
Visualize Application Deviation from Corporate Security Policy
- Identify anomalies in application behavior that may occur before, during or as a follow up after a successful attack
- Insights into deviations such as unauthorized dependency changes, new applications/services/protocols running on the VMs, additions of unauthorized VMs or tearing down of your mission critical VMs, and others.
- Map thousands of cyber threats directly to the anomalous behavior in application performance and dependencies to identify root-cause.
Monitor Lateral Movement of Authorized and Unauthorized Traffic
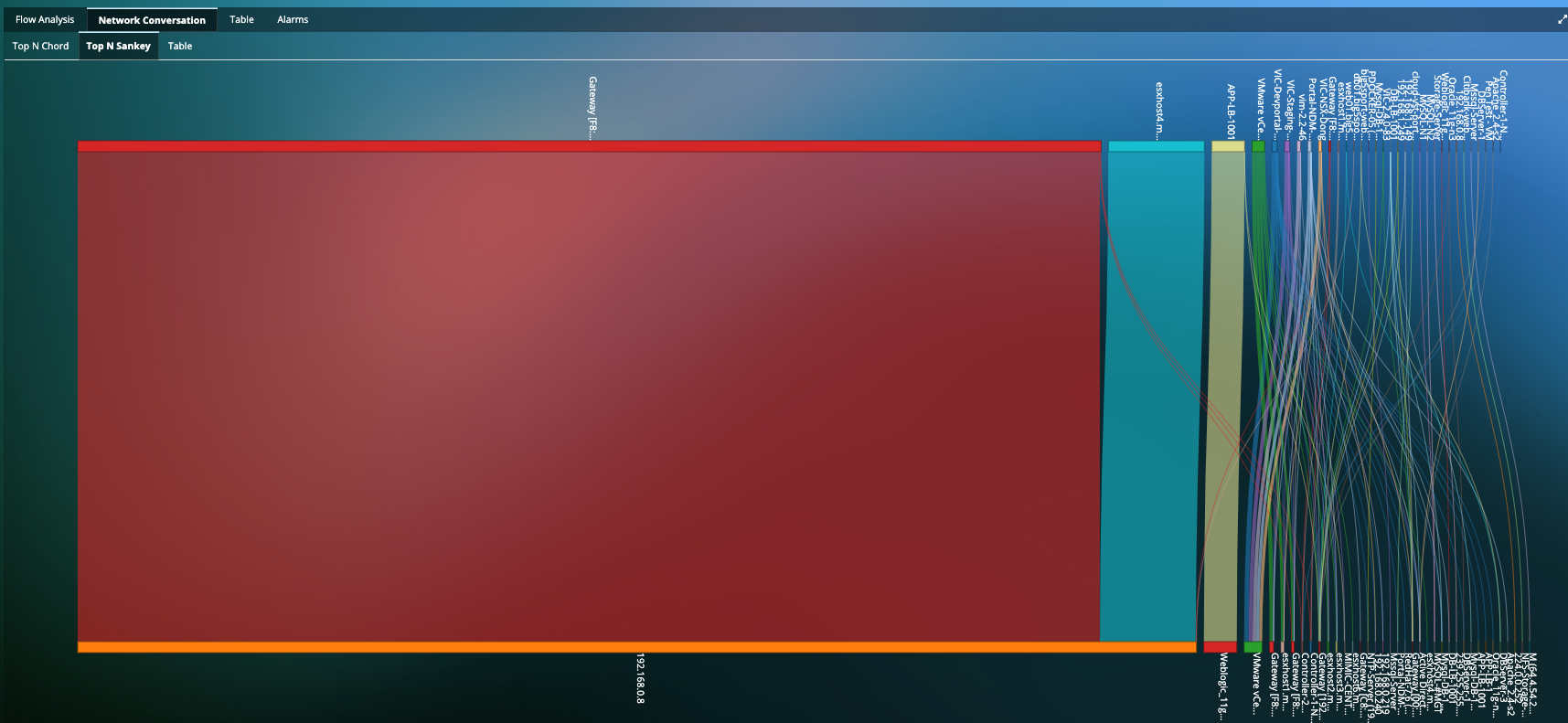
- Deep visualization of a clear indicator of a threat that is attempting to extend its reach into the network.
- Monitor attackers pivoting between compromised hosts to bounce deeper into the network.
- Network Traffic Insights into Network Traffic, Network Response Time, Fatal retries, Resets, Zero Window, etc.
- Application-centric visualization for traffic between servers to provide insight into applications being compromised, or used to compromise.
Resources
-
Cyber Threat Monitoring for the Hybrid EnterpriseQuick 3 minute video that talks about the changing Threat Landscape with attacks moving laterally within the Data Center and Cloud deployments, the importance of identifying Application Anomalous Behavior and Data exfiltration activities and finally on how you can protect your mission critical application workloads with Uila.
-
Application Behavior Anomaly Detection with UilaQuick video on how Uila can identify anomalies in application behavior that may occur before, during or as a follow up after a successful attack.
-
Cyber Threat Detection with UilaQuick video on how Uila can identify advanced cyber threats in your deployment.
-
Lateral Traffic Movement Analysis with UilaQuick video on how Uila can monitor authorized and unauthorized lateral movement or east-west traffic movements within your deployment.
-
Data Exfiltration Analysis with UilaQuick video on how Uila can monitor for outbound traffic from your data center resources to the Internet, that could indicate Data Exfiltration as well as certain Command and Control events.
-
Uila for Webshell Threat DetectionQuick brochure on how to use Uila for Webshell Threat Detection.
-
Uila for Cyber Threat Monitoring Solution BriefQuick solution brief on Uila's Application-centric approach to cyber threat monitoring.
-
Security Analytics and Change Control in the Modern Data Center White PaperRead this white paper to get insights into the security and change control issues of the Modern Data Center.
-
Data Center Security ChallengesIn this blog, we talk about the four critical security challenges IT teams face in any data center.
-
Shadow IT challenge? Take back controlIn this blog we talk about Shadow IT and how organizations can take back control of their own environment and destiny.
-
Wine Producer Success StoryUila Success Story on how a large wine producer solved their Shadow IT challenges.
Ready to begin your Monitoring Journey with Uila?
Start a 21-day Free Trial Now
Request Trial



.jpg)